In a world where data is one of the most valuable corporate assets, improperly deleting it can cost more than the equipment itself that just stopped working. A simple "formatting" or factory reset is often an illusion of security – remnants of information remain, waiting for someone to recover them. Even after recycling old laptops or servers, you can unknowingly share sensitive data, opening the door to data leaks, GDPR violations, and serious legal consequences.
That's why companies that take security and compliance seriously use certified data deletion methods based on recognized standards such as NIST 800-88 guidelines — clearly defining, how to permanently make data irreversible and how to document this process in a legally and audit-acceptable manner.
In this article, we'll explain step by step what "secure data deletion" means, what standards and regulations govern it, what risks ignoring them poses, and what a professional process looks like to ensure that IT equipment leaves a company without a single recoverable bit of information.

What "Securely Delete Data" Really Means (And Why Companies Most Often Get It Wrong)
Many entrepreneurs assume that Deleting data is a simple process – just delete files, format the disk or click "restore factory settings"„ and the problem disappears. Unfortunately, this is very misleading reasoning. In real IT practice „"secure data deletion" means making it permanently impossible to recover information, even using advanced tools or laboratory techniques – and this is the key difference between „removing” and „hiding” data.
Data seemingly disappears, but remains as long as it can be recovered
When you delete a file in the operating system or format a disk, the operating system does not usually physically delete data. What happens is that the space is marked as "free for writing," while the actual information physically remains on the media until it is overwritten. This is what „"data inventory"” – a trace of information remaining after logical operations – constitutes a risk because it can be recovered by data recovery tools or specialized services.
Companies that rely only on standard deletion or formatting often think that the data is already "nowhere", while in practice it is still present on the media and can be read even after the equipment leaves the organization.
„Secure data deletion” is a process, not a single operation
The essence of safe removal is a process that makes data unrecoverable in any realistic way. In practice, this means using methods that meet recognized standards—such as NIST SP 800-88 guidelines—which define how to select techniques appropriate to the type of media and data sensitivity.
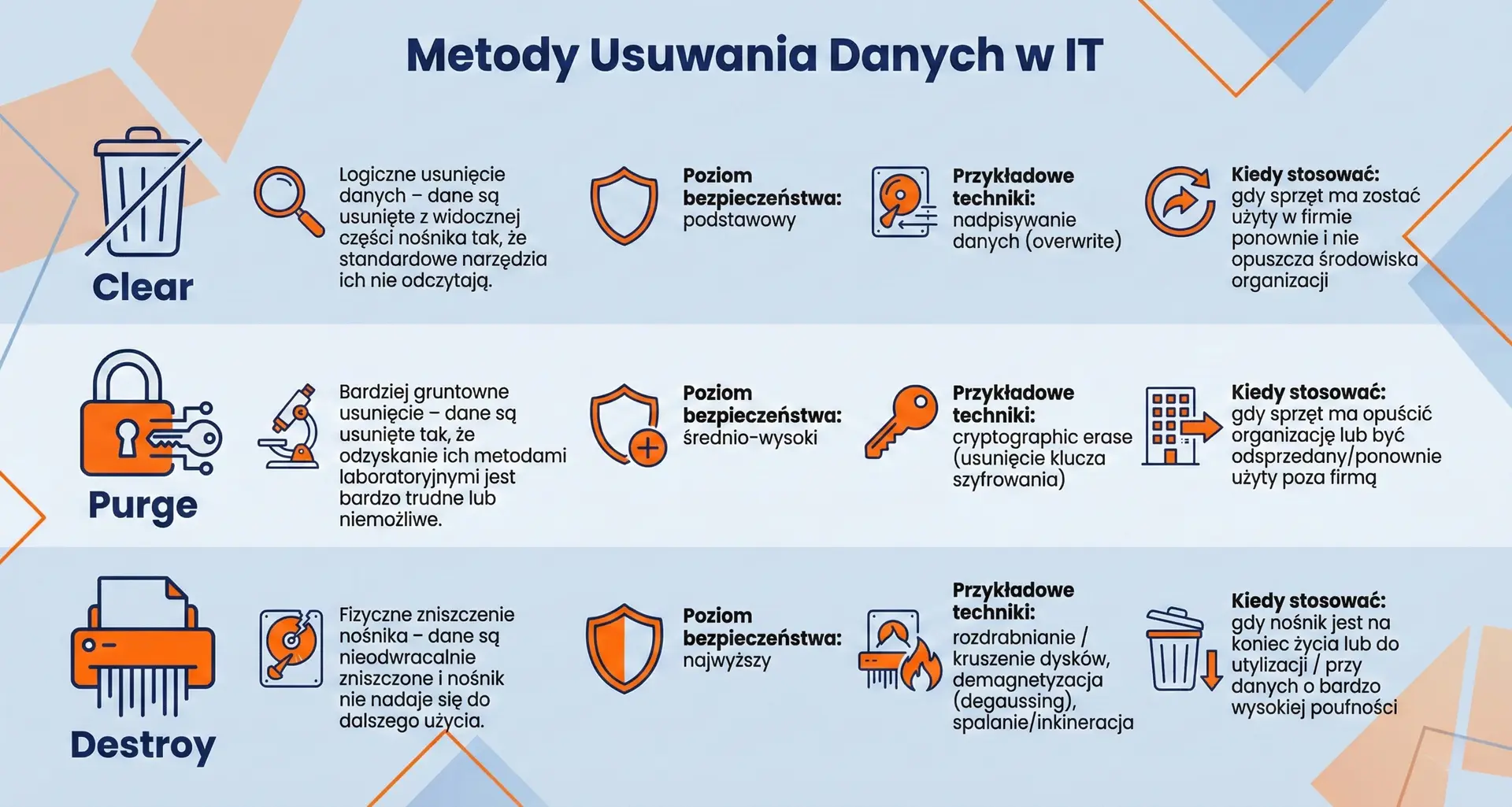
The NIST 800-88 standard indicates that media sanitization should be performed in a manner appropriate to the context of use:
• Clear: simple data deletion that makes it difficult to recover using typical tools but may not protect against laboratory techniques.
• Purge: a more thorough method that significantly limits the possibility of recovery even with advanced tools.
• Destroy: physical destruction of the medium, which makes it impossible to recover data in any possible way.
This classification shows that secure deletion is not just a tool or a click – it is methodical selection of the appropriate sanitization technique depending on the risk and future use of the equipment.
Many companies underestimate the differences between media types
Another common mistake is treating traditional drives (HDD) and modern flash memory (SSD, NVMe) the same. In practice just use the same overwrite method on SSD and HDD, and the effects can be very different - flash media have internal mechanisms, block reorganization and hidden areas that can prevent a standard overwrite from reaching all physical parts of the memory.
„"Secure deletion" also includes verification and documentation
A well-executed data deletion process does not end with the execution of the tool. It is crucial to verify the sanitization effect and document this process – especially if a company wants to demonstrate compliance with regulations and audits. NIST 800-88 and other standards recommend that organizations ensure that no data is accessible after the process and that the actions taken can be documented.
„"Secure data erasure" is much more than just deleting files or formatting. It's a process that aims to permanent and verifiable deletion of information, compliant with recognized standards and controlled by procedures – so that even advanced recovery techniques cannot restore them. Companies often make the mistake of simply deleting data logically does not eliminate residual data or provide proof of its permanent inaccessibility.

NIST 800-88 Standard in Practice – Clear, Purge, Destroy (and when each makes sense)
When we talk about secure data deletion compliant with standards, one of the most frequently cited documents is NIST SP 800-88, "Guidelines for Media Sanitization"„ – a set of practical guidelines developed by the American National Institute of Standards and Technology. This standard does not impose a single "best" method of deletion, but shows how to choose the data deletion method for a specific purpose and type of medium, so that the information cannot be recovered even with advanced techniques..
What is „data sanitization” in NIST 800-88?
According to NIST 800-88, "sanitization" means a process that makes access to data unrecoverable for a given level of effort – that is, it not only makes it difficult, but actually impossible to reproduce information.
This document covers various media technologies – from traditional magnetic disks to modern SSDs, flash memories and mobile devices – and suggests, how to adjust the removal method to real needs organization security.
1) Clear – logical deletion of data (lightest level)
What is this:
The "Clear" method involves deleting data in a logical manner – so that ordinary tools or the operating system cannot read them, but the data can still remain on the medium in a form that can be read by specialized technology.
How it works in practice:
• overwriting data by writing „zeros and ones” or random bits so that any previous information is overwritten;
• restoring the device to factory settings ("factory reset"), often used in smartphones and tablets;
When it makes sense:
• carrier is to be reused in a secure environment within the same organization;
• the data was not highly confidential and did not leave the controlled IT zone;
Good for situations where the computer or disk will be used further – e.g. transferred to another department within the company., But it is not enough if the media is to be disposed of or recycled outside the company.
2) Purge – thorough removal (higher level)
What is this:
„Purge” is a step above Clear – it means deleting data in a way that makes it extremely difficult to recover even using laboratory techniques.
How it works in practice:
• advanced data overwriting with multiple patterns;
• cryptographic erase – deletion or destruction of encryption keys, which makes the encrypted data unreadable;
• special built-in commands such as ATA Secure Erase on HDD/SSD drives or other manufacturer functions that perform sanitization by the media controller;
When it makes sense:
• equipment leaves the controlled IT environment, but may still be used or resold;
• the medium contains medium or high confidentiality data where simple overwriting may not be sufficient;
Purge is used when a device needs to be securely wiped before leaving the company – even if the potential next user has the technical skills to recover data.
3) Destroy – physical destruction (highest level)
What is this:
„"Destroy" is the strongest sanitization method – physical destruction of the medium, which ensures that data cannot be recovered by any technique, even laboratory.
How it works in practice:
• cutting, crushing, crushing or fragmenting memory elements;
• demagnetization (degaussing) – a strong magnetic field removes magnetic recording on HDD platters and tapes;
• incineration or other permanent physical destruction methods.
When it makes sense:
• the carrier will no longer be used and is to be scrapped or recycled;
• contains data about very high confidentiality, which could cause serious damage to the company or its customers in the event of a leak;
When equipment is being disposed of or when data security is a top priority, physical destruction of the media is the last resort.
When to choose which method – practical tips
The choice of method depends primarily on purpose of the medium and level of data confidentiality:
• Clear – suitable when the equipment is to remain within the company and will no longer be used to store sensitive data.
• Purge – the best choice when equipment is about to leave the company, but there is a need for reuse or resale and the data is confidential.
• Destroy – used whenever the medium is to be recycled/disposed of or contains particularly sensitive data.
Why NIST 800-88 is more than just a marketing label„
This standard is widely recognized by organizations around the world not because it is a formal law, but because provides clear criteria for when data can be considered "permanently deleted" and what evidence and processes are needed to document this.
Companies that use NIST 800-88-based procedures find it easier to demonstrate compliance with audits and regulations because they can show not only the result itself, but also justification for the choice of sanitation method and evidence of its implementation.
Standard NIST SP 800-88 does not impose a single recipe for data deletion, but offers a clear framework with three sanitization classes: Clear, Purge, and Destroy, which is selected depending on the risk and intended use of the medium. For companies planning to dispose of IT equipment, this is the foundation of a good process – both in terms of security and subsequent audit verification.
ISO/IEC 21964 (DIN 66399) – standards for media destruction levels and "protection classes"„
When securing data before disposing of IT equipment or company documents, it is worth knowing ISO/IEC 21964 – an international standard defining how to securely destroy information media depending on their confidentiality and type. This standard is based on a German standard DIN 66399 and has been globally adopted as a practical tool for classifying and destroying protected data.
The standard not only says "destroy", but defines the rules for the entire process, from information classification to the selection of appropriate technical means and requirements for media and destruction devices.
Protection Classes – How to Assess How Confidential Your Data Is
ISO/IEC 21964 divides information and data carriers into three classes of protection, which correspond to different levels of confidentiality and the risk of their disclosure:
Protection class 1 – basic protection
This applies to data with a low level of confidentiality, e.g. internal or general information, the disclosure of which would not have serious consequences.Protection class 2 – higher protection (confidential)
This includes confidential data, the unauthorized disclosure of which could negatively impact the company's operations, violate contracts, or jeopardize regulatory compliance (e.g., GDPR).Protection class 3 – very high protection (secret)
It concerns highly sensitive information, the leak of which may have serious legal, business or personal consequences (e.g. strategic data, medical data, technological secrets).
Each of these classes is a starting point for determining what technical and organizational measures should be used in the process of destroying data media.
Media Categories – Different Approaches to Different Media
ISO/IEC 21964 also defines a number of media categories, which is especially important when the company disposes not only of paper but also of electronic devices:
• P - Paper media (e.g. documents, printouts).
• O — Optical data carriers (e.g. CD, DVD, Blu-ray).
• T - Magnetic media (e.g. magnetic tapes, magnetic cards).
• H - Magnetic memory media (e.g. HDD hard drives).
• E - Electronic storage media (e.g. USB, SSD, memory cards, smartphones).
• F - Miniature media (e.g. microfilms).
For each category of media, the standard specifies what destruction methods and what size of fragments (cuts) are considered to be compliant with a specific level of protection.
Seven levels of security – how „hard” you have to destroy
Each protection class is matched to security levels, determined from 1 to 7 — the higher the level, the smaller fragments must be crushed into smaller pieces, which makes it difficult or impossible to restore data after destruction.
• Level 1–3 – usually sufficient for low or medium sensitivity data.
• Level 4–7 – intended for confidential and particularly sensitive data; the higher the number, the smaller the fragments, e.g. microscopic pieces, which make it impossible to reconstruct the content.
For example, for paper media:
• P-1 – strips up to approx. 12 mm wide,
• P-5 – very small fragments with an area of up to approx. 30 mm²,
• P-7 – the smallest fragments with an area of approximately 5 mm² or smaller – used for highly confidential data.
For electronic media or HDDs, the levels define the minimum fragmentation or deformation parameters required for a given protection class, so that data recovery is practically impossible.
How it works in practice – an example for IT equipment
In the context of IT equipment disposal, the standard helps to determine, how small fragments need to be obtained to meet safety requirements. For example, for sensitive media (e.g. HDD or memory cards containing customer personal data) a level of H-4 and above, which generates fragments of data that are difficult to recreate without a specialized laboratory.
Establishing the appropriate level of security after data analysis means that a company can demonstrate with a high degree of certainty that the destruction process was in line with a recognised global standard – which also has audit and legal significance (e.g. in the context of GDPR).
Why ISO/IEC 21964 matters to businesses
ISO/IEC 21964 provides more than just technical guidance on media fragmentation. This standard:
• helps categorize data and media according to confidentiality and risk levels,
• indicates optimal technical parameters of destruction,
• creates the basis for documenting and justifying security activities,
• facilitates compliance with audit requirements and personal data protection regulations.
For companies planning to dispose of IT equipment, this standard provides an independent point of reference – both when they carry out the process themselves and when they outsource it to an external service provider.
ISO/IEC 21964 (formerly DIN 66399) This comprehensive standard describes how to classify data according to its confidentiality, how to define media categories, and what security levels to apply during physical data destruction. Applying this standard in practice helps companies establish secure, best-practice disposal processes for IT equipment and other data media – a key issue not only technically but also from an audit and legal perspective.


Regulations and obligations of companies in Poland and the EU – GDPR, e-waste, BDO
The process of disposing of IT equipment is not only about the technical aspects of secure data removal – companies must also take care of compliance with applicable legal regulations both regarding personal data protection and environmental protection. Below you will find compact and specific overview the most important requirements that apply to entrepreneurs in Poland and the European Union.
GDPR – obligation to permanently delete data, also at the disposal stage
GDPR (EU Regulation 2016/679) imposes on companies the obligation to use technical and organizational measures to ensure an appropriate level of personal data security, taking into account the risk for the rights and freedoms of data subjects. In practice, this also means that data deletion from media before disposal must be effective and verified – so as to prevent unauthorized access or recovery of information after the equipment is returned. The GDPR does not provide specific methods, but clearly requires that the data be permanently deleted in accordance with the principles of processing security and so that the administrator can document it.
Key consequences:
• The data controller must demonstrate that he has taken appropriate measures deleting data before disposing of equipment.
• Lack of proper sanitation procedure may result in liability for data protection violations, regardless of the subsequent disposal of the equipment.
Electronic waste and the WEEE directive – the EU framework and the obligations of Member States
At the EU level it applies WEEE Directive (Waste Electrical and Electronic Equipment Directive, 2012/19/EU) – a legal act that forces member states to organize systems for collecting, processing, recycling and disposing of e-waste. E-waste is electrical and electronic devices that have become are useless and are thrown away, e.g. computers, monitors, telephones or routers.
The WEEE Directive assumes, among other things:
• duty organization and financing of the collection and processing of used equipment from producers or importers,
• achieving specific collection and recycling levels for various categories of equipment,
• keeping records and reporting the quantity of equipment introduced to the market and sent for recycling.
Although WEEE is a directive (i.e. the EU legal framework), in Poland its provisions are implemented by national legal acts, which impose specific obligations on entrepreneurs participating in the electronic equipment market or generating e-waste.
BDO – waste records and entrepreneur's obligations
In Poland, the superior system for waste management, including e-waste, Is BDO – Database on Products, Packaging and Waste Management, which results from, among others, Waste Act and the Act on Electronic Waste (WEEE).
Who must work in BDO?
If a company introduces electrical and electronic equipment to the market, generates waste other than municipal waste (e.g. e-waste) or intends to dispose of it, it is often must register in the BDO system and obtain a registration number.
Obligations of companies in practice
• Registration with BDO – the entity generating waste or managing equipment must have an account with a registration number.
• Waste records – obligation to keep electronic records of waste quantity and quality in the BDO account, with appropriate waste codes.
• Accompanying documents – each transfer of e-waste to a professional recipient must be documented Waste Transfer Note (WTP) or other documents provided for in BDO.
• Transfer only to authorized recipient – used equipment should be sent to entities with appropriate permits that maintain their own records in BDO.
Penalties and consequences
Lack of registration, lack of records, incorrect documents or handing over of electronic waste to an unauthorized entity may result in administrative penalties (high fines) and problems during environmental inspections or audits.
How does this fit together in practice?
For a company disposing of IT equipment, there are often three areas of responsibility simultaneously:
• secure data deletion in accordance with GDPR,
• handing over the equipment as electronic waste in accordance with WEEE and national regulations,
• keeping records and documentation in the BDO system.
This means that the disposal process should be planned to meet all these requirements – not only to secure data, but also to comply with environmental protection and waste accounting laws.
To sum up:
• GDPR imposes the obligation to permanently delete data from media before they are disposed of – this is a matter of information security and compliance with personal data protection.
• WEEE Directive (EU) and its implementation in Poland means that electronic equipment cannot be thrown away like regular garbage – companies must take care of its collection, recycling or disposal.
• BDO is a central waste registration system in Poland – registration, recording and documenting the flow of electronic waste is a condition for the proper disposal of IT equipment.
This comprehensive approach allows the company not only secure data and the environment, but also avoid the risk of fines and problems during inspections.
What does a secure IT disposal process look like step by step (from inventory to certification)
1) Equipment inventory and classification
The first step is complete identification of devices intended for disposal. Record the model, serial number, location, data sensitivity, and equipment suitability assessment (whether it is suitable for reuse, sale, recycling, or safe disposal).
Key activities:
• Create a detailed equipment list with unique identifiers.
• Determining the level of confidentiality of data on devices.
• Registering equipment in the IT asset management system (ITAM).
2) Planning and risk assessment
Based on the inventory, an inventory is created. action plan, including data disposal and destruction methods adapted to the type of media and the level of confidentiality of the information, as well as an assessment of the risk associated with each device.
Key activities:
• Determining sanitization methods for disks, SSDs, flash memory, etc.
• Schedule of activities and transport rules.
• Assess which devices can be safely resold or donated.
3) Backup and migration of important data
Before the secure data deletion process begins, a backups of information that is still needed, and migration to a new environment or archive.
Key activities:
• Data backup business and operational.
• Confirmation of the integrity of saved data after migration.
4) Data deletion (sanitization/destruction)
This the most important stage, in which data is permanently eliminated from media in accordance with agreed methods (certified data erasure, demagnetization or physical destruction). The aim is ensuring that data cannot be recovered by any technique.
Example techniques:
• Software for secure data deletion (overwriting, crypto erase).
• Demagnetization (degaussing) – demagnetization of magnetic media.
• Physical destruction of media (cutting, crushing).
• Verification of the effect using auditable methods.
5) Transport and chain of custody
Equipment intended for disposal or recycling should be transported in a controlled manner and provided with chain of responsibility documentation, so that each movement is documented and auditable.
Key activities:
• Securing equipment in sealed containers.
• Recording the transfer of devices with the signatures of the responsible persons.
6) Segregation and recycling / physical disposal
After deletion of data, it is segregation of hardware components: components suitable for reuse, recycling, or safe disposal. In this step, specialists separate metals, plastics, batteries, and other parts in accordance with environmental protection principles and e-waste regulations.
Key activities:
• Separation of recyclable materials.
• Protection and disposal of hazardous elements (e.g. batteries, toners).
7) Documentation and certification
At the end of the process, the recycling company should deliver full documentation confirming the activities performed, including data destruction certificates, sanitization protocols, and documents required by waste management regulations (e.g., waste transfer notes). This is a key element for both GDPR compliance and internal and external audits.
Key activities:
• Certificate confirming the deletion of data or physical destruction of media.
• Report on the transfer of electronic waste to an authorized recipient.
• Any documents confirming recycling or recovery of raw materials.
Process Summary:
Secure IT disposal is cyclical and fully documented procedure, which begins with asset identification, continues with planning and data disposal, and continues with recycling and certification. This structured process minimizes the risk of information leakage, meets regulatory requirements, and provides the company with solid evidence of compliance and professionalism.

How to choose a contractor so as not to buy "paper without security"„
Choosing a partner for IT equipment disposal is a decision with a high risk burden – both cybersecurity and regulatory compliance. A bad contractor may only provide a declaration without real security measures or a certificate that there is no coverage in the audited processes. Below you will find a condensed list of key criteria, that help distinguish a reliable service provider from a "paper supplier"„.
1) Data erasure certificates are the foundation
A declaration of "compliance with standards" is not enough - check whether the supplier has formal certificates confirming audited processes.
• NAID AAA – the global standard for secure data destruction services; audits processes, equipment, procedures and documentation.
• R2v3 (Responsible Recycling) – a certificate for electronics recycling organizations, covering data sanitization, working with subcontractors and environmental management.
• ISO 27001 – confirms that the contractor has an information security management system in place (e.g. policies, access controls, documentation processes).
These certificates are proof that the company not only knows the standards, but actually implements them and undergoes audits.
2) Chain of custody – essential for security
Ask about procedures for equipment supervision chain from receipt to destruction. If the contractor:
• seals and secures the equipment upon receipt,
• tracks it with serial numbers at every stage,
• will document each transfer,
This significantly reduces the risk of data media being lost, stolen, or accidentally leaked. It is the lack of such evidence that often causes companies to formally they cannot prove compliance with GDPR or audit.
3) Documentation and certificate of service performance
A good contractor must provide you protocol/proof of data deletion on the level single carrier (e.g. with the disk serial number). The documents should clearly describe:
• what method was used (e.g. purging, physical destruction according to NIST 800-88),
• what standard/certificate is the basis for the action,
• who, when and how performed the operation.
Such a certificate is audit evidence, which you can present in internal or external audits.
4) Check compliance with technical standards
The service provider should work in accordance with recognized data sanitization standards, e.g.:
• NIST SP 800-88 – defines the Clear, Purge, Destroy methods that help estimate the technical risk of the operation.
• ISO/IEC 21964 / DIN 66399 – determines the security levels of physical destruction of media (types of cuttings, etc.).
Make sure the contractor not only knows these standards, but applies them in practice and can document it.
5) Evaluation of subcontractors and the entire chain of proceedings
A professional partner not only performs the operations himself, but also selects its subcontractors in accordance with procedures (e.g. recycling plants, transport). This means:
• thorough verification of subcontractors,
• monitoring their certificates and compliance,
• documenting the entire media flow.
The lack of such verification is a common reason why a nominally „certified” process is actually not secure.
6) Liability insurance and audit support
A good contractor should offer liability insurance for damage caused during the disposal process, e.g. as a result of an error or incident.
Additionally, services in which the partner is helps prepare documentation and answer audit or GDPR control questions – this significantly increases the value of cooperation.
Key questions for a potential contractor
Before you sign a contract, it is worth asking questions such as:
• What certificates does the company have and can you see them?
• How does it document the equipment chain of custody?
• Does it issue a certificate of destruction with unique media identifiers?
• What data sanitization standards does it use and how does it verify them?
• How do subcontractors and their certificates get verified?
• Does it offer liability insurance and audit support?
To sum up,
When choosing a data disposal and secure deletion contractor, don't just look at declarations and general promises - search specifics: certificates, documented processes, equipment tracking and audit evidence. Only then can you be truly certain that the process is safe, compliant with regulations, and based on international standards, not just "paper assurances.".
Frequently asked questions
Yes – if the equipment contains personal data (e.g. customers, employees), it must be permanently delete or destroy them so that they cannot be recovered in accordance with the principle of storage limitation and data minimization. Standard file deletion or formatting is not always enough, because the data may remain on the medium and be recovered using specialized tools.
No. Only permanent data sanitization – for example, overwriting in accordance with standards (such as NIST 800-88) or physically destroying the media – ensures that the data cannot be recovered. Formatting leaves the data on the media in a form that can be reconstructed by advanced tools.
A professional contractor should provide you with:
certificate or protocol of data deletion,
confirmation of the type of method used (e.g. overwriting or destruction),
media serial number or other identifier,
documentation compliant with audits and possible GDPR controls.
This gives you proof that the process was performed correctly and in accordance with good practices.
If your company generates non-municipal waste (e.g. e-waste from computers, phones, printers), it is usually you must register with BDO – Database of Products, Packaging and Waste Management and record the transfer of equipment for disposal or recycling.
BDO is the central waste registration system in Poland, which allows you to supervise how entrepreneurs they manage waste – from their creation to their transfer for recycling or disposal. If you do not register with BDO or do not maintain the required documentation, you may be exposed to high financial penalties, and activities related to the collection and disposal of waste may be considered illegal.
We offer comprehensive support for companies – from equipment inventory, By certified data deletion in accordance with the best standards, until safe collection, disposal and BDO documentation. We provide full confirmation of completed activities, which you can use in audits, GDPR checks, or environmental reporting.
Securely erasing data before IT equipment disposal isn't a "technical detail," but a component of real risk management within a company. Formatting or restoring factory settings alone doesn't guarantee that information won't be recovered. Only the conscious application of standards such as NIST 800-88 and ISO/IEC 21964, combined with proper documentation and compliance with GDPR and BDO, creates a process that is defensible both technically and audit-wise.
Well-planned IT disposal is a combination of three pillars:
• the right method data sanitization,
• chain of responsibility control,
• complete documentation confirming the performance of the service.
It's not just a matter safety information, but also company reputation, management accountability, and regulatory compliance. The equipment may be "old," but the data stored on it still holds value—to you or to someone trying to recover it.
If this topic concerns your company and you'd like to streamline your IT disposal process in a secure, compliant, and well-documented manner, please get in touch. We'd be happy to help you through it step by step.